
Published for CIOs, IT Directors & Security Leaders | Estimated Read: 14 min
The breach has happened—but the real risk begins now. Most organizations underestimate what comes next. The post-attack phase is where systems either become stronger or remain vulnerable to repeat breaches. This is where an IT maintenance services company plays a critical role, handling recovery, system hardening, and long-term IT security maintenance to prevent future attacks.
Studies show that over 60% of organizations experience a second cyberattack within a year if post-breach remediation is incomplete.
The average cost of repeat breaches is significantly higher due to compounded system vulnerabilities and operational downtime.
According to IBM's Cost of a Data Breach Report, organizations that fail to fully remediate after an attack face a 26% higher likelihood of a repeat breach within 24 months. The recovery phase is where long-term security is won or lost.
This guide is built for CIOs, IT Directors, and Security Leaders who need a precise, actionable roadmap — not generic advice. From Week 1 stabilization through long-term hardening, we cover every phase of post-breach IT maintenance with the depth your decisions require.
An IT maintenance services company manages post-breach recovery by validating threat removal, rebuilding compromised systems, implementing system hardening, and establishing continuous monitoring. Their role ensures organizations not only recover from cyberattacks but also reduce the risk of repeat incidents through ongoing IT security maintenance.
Not all IT support providers are equipped for this work. A specialist, reliable IT maintenance company brings dedicated post-breach engineering capability, structured recovery frameworks, and embedded security operations — far beyond what a standard helpdesk or generalist MSP can deliver.
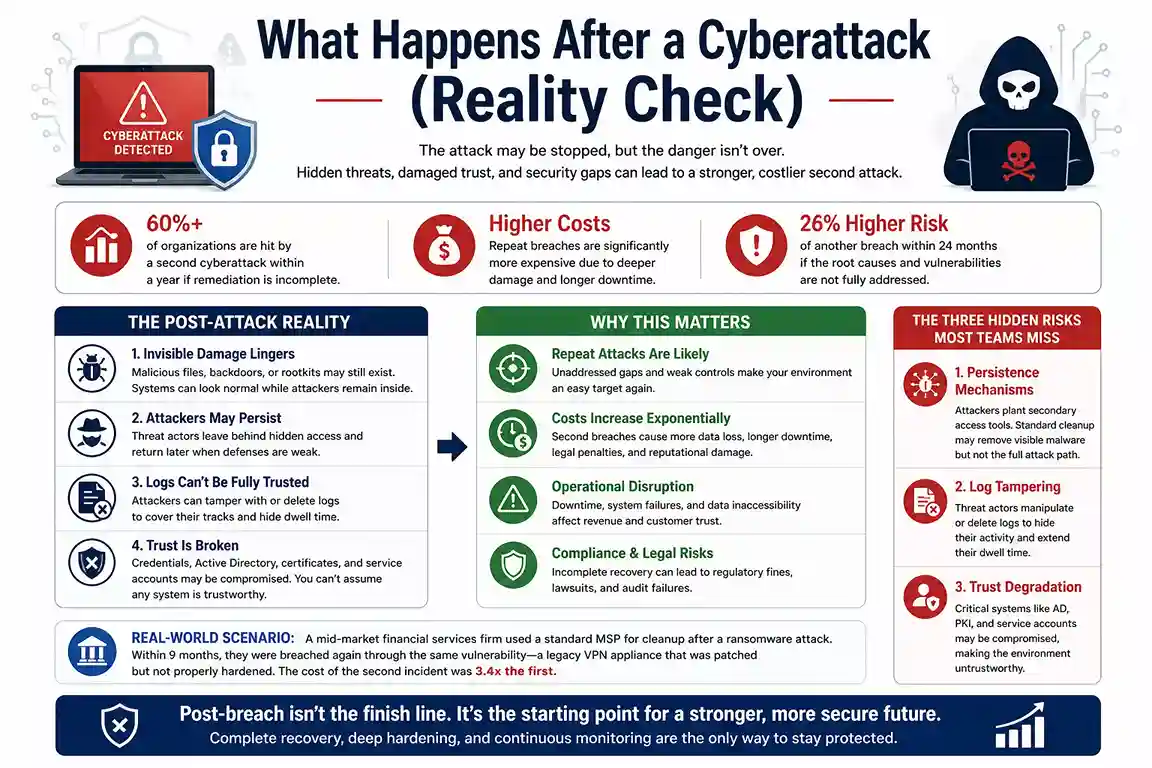
Most executives assume the hard part is over once the attacker is expelled. That assumption is catastrophically wrong.
Cyberattacks — whether ransomware, supply chain compromise, or credential-based intrusions — leave invisible damage across your infrastructure. Systems appear functional but may be running compromised binaries. Credentials appear rotated, but backdoors may remain. Endpoints appear clean, but rootkits can survive standard reimaging.
This is the reality that separates organizations that fully recover from those that become repeat victims. The post-breach environment cannot be treated as "mostly fixed" — it must be treated as compromised until proven otherwise through rigorous IT security maintenance.
Real-World Scenario: A mid-market financial services firm engaged a standard MSP for cleanup after a ransomware event. Within 9 months, they experienced a second breach via the same initial access vector — a legacy VPN appliance that had been patched but not fully hardened. The cost of the second incident was 3.4x the first.
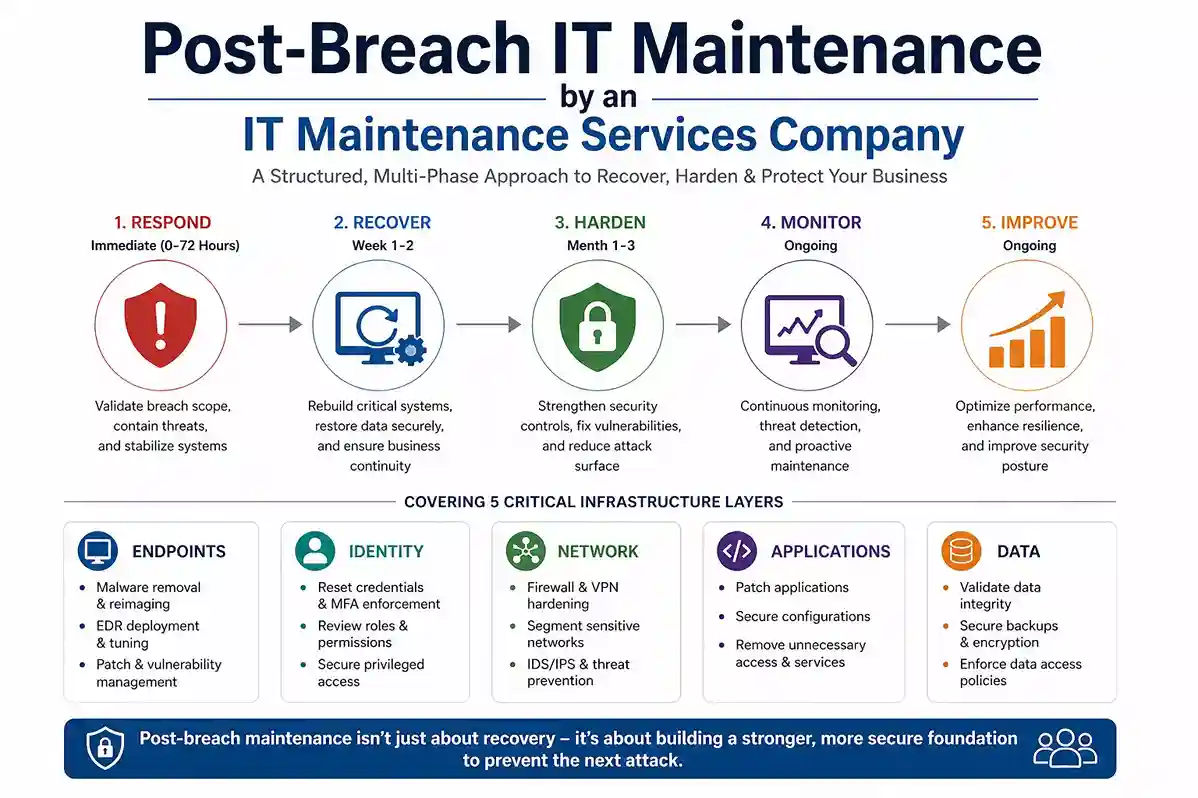
Post-breach IT maintenance is a structured, multi-phase discipline that addresses five distinct infrastructure layers: endpoints, identity, network, applications, and data. It is fundamentally different from both standard IT operations and incident response.
| Focus | Contain the attack | Rebuild & validate systems | Maintain uptime |
|---|---|---|---|
| Goal | Remove the attacker | Harden the environment | Routine operations |
| Activity | Preserve forensic evidence | Establish continuous monitoring | Helpdesk & service desk |
| Timeline | Days to weeks | Months to ongoing | Perpetual cycle |
| Owner | IR/forensics firm | IT maintenance services company | Internal IT / MSP |
Understanding how IT maintenance during business hours differs from after-hours incident response is critical for continuity planning. Structured post-breach maintenance spans both windows and cannot be limited to a standard support schedule.
General IT support teams are built for operational continuity — not for the forensic rigor and security engineering discipline that post-breach environments demand. Here is why a specialist IT maintenance services company is non-negotiable after a significant breach:
Organizations with a retained IT security maintenance partner detect follow-on threats 74% faster than those relying on ad-hoc incident response engagements.
Engaging a dedicated IT maintenance services company after a cyberattack delivers measurable, sustained advantages that in-house teams and generalist providers cannot replicate.
| Faster Recovery | Structured phase-gated methodology reduces time-to-stable from months to weeks |
|---|---|
| Lower Repeat Breach Risk | Systematic hardening closes the attack vectors that enabled the original incident |
| Continuous Threat Visibility | 24/7 SOC and SIEM monitoring detects follow-on threats before they escalate |
| Regulatory Compliance | Maintained security controls support HIPAA, PCI-DSS, ISO 27001, SOC 2 requirements |
| Reduced Total Cost | Early engagement and ongoing maintenance costs far less than a second breach |
| Board-Level Confidence | Executive reporting translates technical security posture into risk metrics leadership understands |
| Institutional Memory | Your provider retains full context of the breach, recovery, and hardening — critical for future response |
Partnering with the right provider is not a cost center decision — it is a risk management investment with a quantifiable return.
Cyber recovery services encompass the technical and strategic activities required to restore full, verified operational capability following a security incident. Here is how a structured IT maintenance services company phases the engagement:
Key Deliverable (Week 1-2): A validated clean baseline image for all Tier 1 systems, confirmed via EDR tooling and independent hash verification.
Use this checklist to confirm all critical activities are complete before declaring your environment stable:
System hardening is the most technically demanding phase of post-breach recovery — and the one most organizations shortcut. A dedicated IT maintenance services company applies CIS Benchmarks, NIST SP 800-53, and DISA STIGs as structured frameworks, not suggestions.
You cannot harden what you cannot see. Conduct a full asset discovery sweep across on-premises, cloud, and hybrid environments. Classify every asset by sensitivity, criticality, and attack surface exposure before any hardening work begins.
Run authenticated vulnerability scans across all discovered assets. Prioritize using CVSS scores combined with real-world exploitability context — a high-CVSS finding with no external exposure ranks lower than a medium-CVSS finding on an internet-facing service.
Establish a risk-based patch management cadence: critical vulnerabilities within 24-48 hours, high-severity within 7 days, medium within 30 days. Automate wherever operationally feasible. This discipline directly addresses technical debt challenges that accumulate in under-resourced IT environments and become the next breach's entry point.
Hardening without validation is theater. Conduct post-hardening penetration testing to verify every control is effective against real-world attack techniques. Document the hardened state as a new certified baseline for all future change management processes.
Recovery is a milestone, not a destination. The organizations that avoid repeat breaches are those that transition from reactive cleanup to proactive IT security maintenance, sustained continuously by a dedicated IT maintenance services company.
| Monitoring | SIEM alerting, EDR threat hunting, anomaly detection | 24/7 continuous |
|---|---|---|
| Vulnerability Management | Authenticated scanning, CVE tracking, risk scoring | Weekly scan / Monthly review |
| Patch Management | OS, application, firmware patching with rollback | Per-severity SLA |
| Identity Governance | Access reviews, PAM audit, MFA enforcement checks | Quarterly |
| Incident Readiness | Tabletop exercises, IR plan updates, backup validation | Semi-annual |
Enterprise cyber recovery maintenance services integrate all five pillars under a unified framework with defined SLAs, escalation paths, and executive reporting — not as disconnected point solutions.
Our DevOps consulting services integrate security maintenance directly into CI/CD pipelines and operational workflows, ensuring resilience is built into the development lifecycle — not retrofitted afterward.
For organizations navigating digital transformation failure risks, security maintenance must be incorporated into the rebuild architecture from day one — not added after systems go live.
Organizations should engage an IT maintenance services company immediately after a cyberattack, during major system upgrades, or when recurring vulnerabilities are detected. Delaying post-breach maintenance increases the risk of repeat attacks, data loss, and compliance failures.
The earlier an IT maintenance services company is engaged post-breach, the lower the total remediation cost. Delaying engagement by 30 days can double remediation complexity and significantly extend the exposure window.
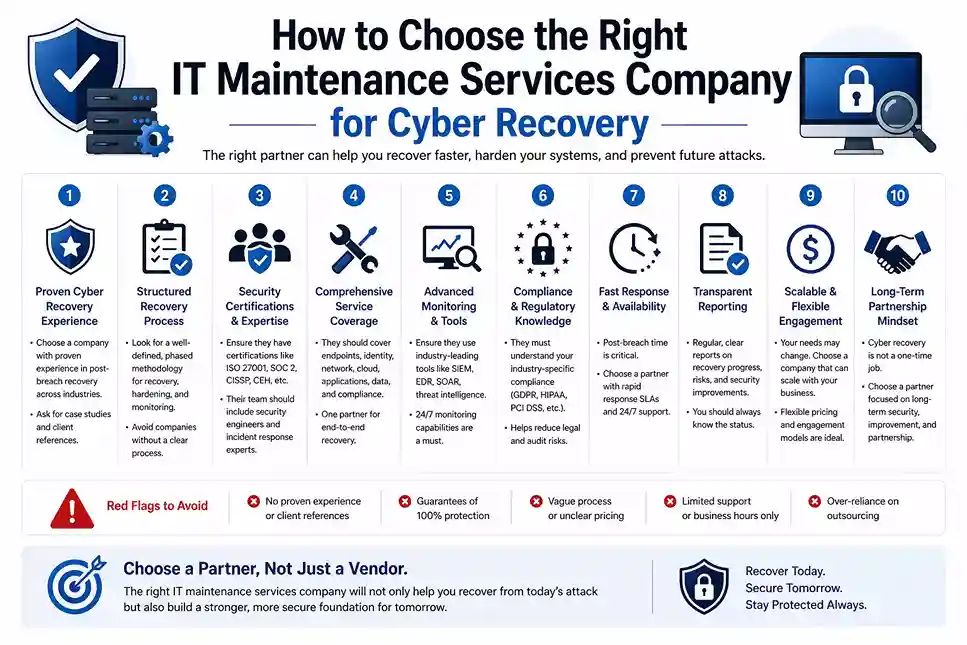
Not every IT provider is equipped for post-breach work. Use these criteria to evaluate candidates with the rigor the decision deserves.
Critical Red Flag: Any provider who proposes to "clean" a compromised Active Directory environment without first establishing the full forensic scope of the compromise. This single shortcut is the most documented driver of repeat breaches.
Backups created during or after the attacker's dwell period may contain malware or backdoors. Always validate backup integrity against known-clean checksums before any restoration. Establish backup immutability using WORM (write-once, read-many) storage going forward.
Patching removes known vulnerabilities. It does not remove attacker-planted tools, hidden backdoors, or compromised credentials. Post-breach environments must be rebuilt or forensically validated — patching alone is never sufficient.
Active Directory compromise is frequently total. If forensics cannot confirm the precise scope of AD access, assume full compromise and rebuild from scratch. Attempting to "clean" a compromised AD forest typically fails and extends the exposure window significantly.
Organizations consistently spend the majority of post-breach budgets on prevention and almost nothing on detection capability. Without a functioning SIEM or MDR service, the next attacker will operate undetected for weeks before discovery.
Post-breach recovery requires embedded collaboration between IT operations and security engineering — ideally unified under a single IT security maintenance consulting provider. Neither team succeeds in operating in isolation post-breach.
The post-incident review (PIR) is the single highest-value activity after any breach. It documents the timeline, root cause, contributing gaps, and corrective actions required. Organizations that skip it are statistically likely to repeat the same mistakes.
Critical Insight: Repeat breaches are not bad luck. They are predictable outcomes of incomplete remediation. Understanding the recurrence pattern is the first step to breaking it.
Without full attack path reconstruction, persistence mechanisms — scheduled tasks, WMI subscriptions, compromised firmware — survive standard incident response and reactivate weeks or months later.
Remediation that does not address the initial access vector leaves the same door open. Attackers frequently share or sell access to previously compromised environments on criminal forums and darknet marketplaces.
Post-breach organizations temporarily intensify monitoring, then relax as operational pressures return. Without sustained managed monitoring from a retained IT maintenance services company, the detection window widens, and attackers find renewed opportunity.
Many organizations address the immediate breach impact but defer underlying technical debt challenges — legacy systems, unpatched appliances, shadow IT assets — due to budget or operational constraints. These deferred items consistently become the next breach's initial access vector.
Organizations that engage a one-time IR firm and then revert to their pre-breach provider lose all continuity of context. Retaining an ongoing IT maintenance services company with security embedded in scope eliminates this gap entirely — and provides the institutional memory that makes faster future response possible.
If your organization has experienced a cyberattack — or wants to ensure it never happens again — partner with a trusted IT maintenance services company. From cyber recovery services to system hardening and continuous monitoring, the right partner ensures long-term protection and operational resilience.
The organizations that break the breach cycle share one common characteristic: they retained a specialist who treated post-breach recovery as a structured engineering program — not a cleanup project. They invested in hardening, monitoring, and continuous improvement rather than returning to the status quo that enabled the breach.