
A regional hospital network had passed its HIPAA audit three years running. Then the OIG examiner asked a question nobody in the room could answer: "Where, exactly, is your patient data being processed during your SaaS vendor's maintenance windows?"
The compliance officer reached for the vendor contract. The legal team called their account manager. The CISO opened a thirty-page terms-of-service document. After forty-five minutes, the honest answer was: nobody knew.
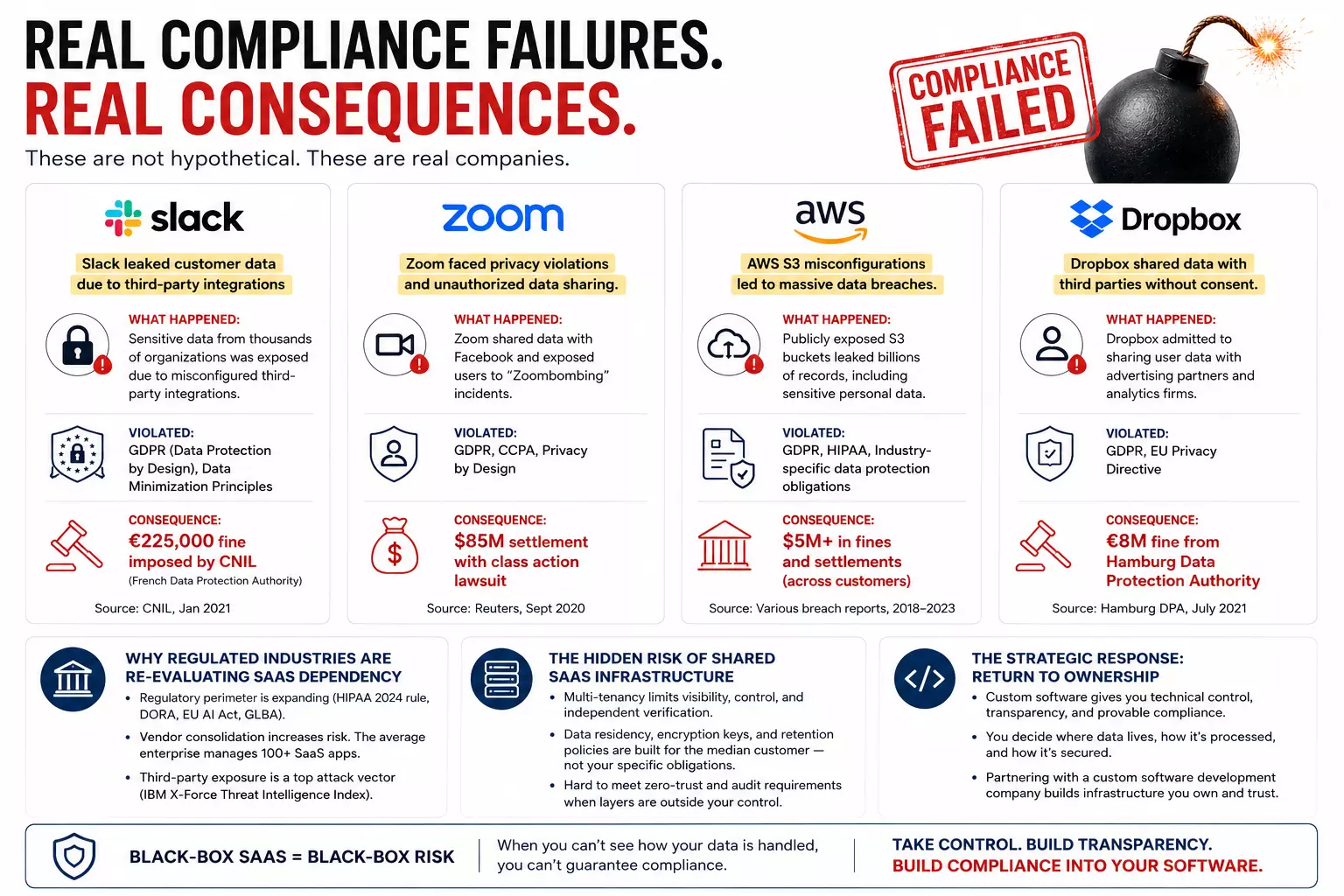
That single gap — not a breach, not a misconfiguration, not even a policy violation — triggered a corrective action plan, a six-month vendor reassessment, and a board-level conversation about whether their commercial SaaS platform could continue to underpin their most sensitive medical workflows. It is exactly the kind of scenario now prompting CIOs throughout healthcare, financial services, and government contracting to revisit an option many had written off as cost-prohibitive: working with a custom software development company to build infrastructure they actually own and control.
The term "black-box SaaS" is not an indictment of commercial software quality. Most enterprise SaaS platforms are engineered competently. The problem is structural, not technical.
When a regulated organization subscribes to a multi-tenant SaaS platform, it accepts a fundamental bargain: operational convenience in exchange for visibility. The vendor controls the runtime environment, the data pipeline, the update cadence, the subprocessor relationships, and — critically — the audit log architecture. The customer's access to this infrastructure is contractual, not technical. They can ask. They cannot verify independently.
Regulators under HIPAA, GLBA, SOC 2 Type II audit protocols, and emerging EU AI Act obligations are asking questions that require technical answers — answers that many SaaS contracts are simply not built to provide.
During a compliance review of a mid-market insurance carrier, the security team discovered that the carrier's claims management SaaS vendor had migrated data processing to a new cloud region without notifying customers. The change was permitted under the terms of service. It violated the carrier's own data residency policy.
The re-evaluation is not driven by nostalgia for on-premise systems. It is driven by a convergence of regulatory pressure, vendor consolidation risk, and a maturing understanding of where SaaS multi-tenancy introduces unacceptable exposure.
DORA now requires financial entities to maintain audit and inspection rights over ICT third-party providers — a threshold many standard SaaS contracts do not meet. HIPAA's strengthened enforcement under the 2024 proposed rule updates places a greater burden on covered entities to demonstrate active oversight of business associates, rather than passive reliance on BAAs.
Gartner has noted that the average enterprise now manages over 100 SaaS applications — each signifying a vendor relationship, a data-sharing agreement, and a potential audit finding. The platform your organization depends on today may be acquired or sunset within a 24-month window.
IBM's Security X-Force Threat Intelligence Index has consistently identified third-party exposure as a top attack vector for enterprise breaches. Your security posture is partly determined by decisions you did not make and cannot inspect.
The following scenarios reflect patterns detected in enterprise compliance engagements.
A financial services client discovered during a SOC 2 Type II audit that their HR analytics SaaS vendor had enabled a third-party AI enrichment layer on employee data — opt-out, buried in a changelog. The client had, unawares, shared sensitive workforce data with a subprocessor they had never assessed.
A government contractor undergoing FedRAMP authorization found that its project management SaaS did not support FIPS 140-2-validated encryption across all API endpoints. The vendor placed a fix on an eighteen-month roadmap. The contractor was left choosing between a compliance waiver and a mid-project platform migration.
One healthcare provider requested full data deletion verification from their EHR SaaS vendor following a patient records purge. The vendor could not confirm backup purge timelines across all regional data centers. The audit finding: "insufficient evidence of data destruction."
These are not edge cases. They are the predictable consequence of deploying black-box infrastructure where the regulatory expectation is technical accountability, not contractual assurance.
Multi-tenancy is the architectural foundation of commercial SaaS economics — and the source of its deepest compliance tension.
In a shared-infrastructure model, the vendor's application layer enforces logical separation between customer environments. Misconfiguration incidents, privilege escalation vulnerabilities, and cross-tenant exposure events, while rare, are not theoretical. More practically, your organization's data sovereignty, encryption key management, and retention policies are built on a framework constructed for the median customer—not your specific regulatory obligations.
Zero-trust architecture principles — a baseline expectation under NIST SP 800-207 and referenced in both the FedRAMP and CMMC frameworks — mandate explicit verification at every access layer. Shared SaaS infrastructure makes this difficult to implement comprehensively, because several of those layers are outside the customer's technical perimeter.
Data sovereignty has moved from a procurement concern to a board-level strategic question. The GDPR's Schrems II implications, the India DPDP Act, and the expanding patchwork of data localization requirements have created a compliance landscape where "Where is our data?" must be answerable with technical exactness, not vendor assurance.
Custom software development for data sovereignty is not simply about hosting data on-premises. It is about designing systems where data classification, residency controls, and processing boundaries are encoded at the architectural level—not managed through vendor settings that can change with a product update.
This is where the debate around custom software vs SaaS security becomes operational rather than theoretical. The difference becomes clearest when evaluated through a compliance governance lens — where the question is not which platform performs better, but which architecture can be held accountable.
| Audit evidence | Vendor-generated; scope limited by contract | Full technical evidence; organization-controlled |
|---|---|---|
| Data residency | Vendor-defined; may change with product updates | Architecture-encoded; jurisdiction-specific by design |
| Encryption key management | Vendor-managed or shared KMS | Organization-controlled; HSM integration possible |
| Subprocessor transparency | Disclosed contractually; may expand without notice | No third-party data pipeline unless explicitly designed |
| Regulatory update response | Vendor roadmap; timeline not guaranteed | Immediate, scoped to specific compliance requirement |
| Zero trust implementation | Partial; bounded by platform architecture | Full implementation across all application layers |
| Breach containment perimeter | Shared with other tenants | Fully isolated; breach radius defined by your architecture |
Organizations that successfully transition from non-compliant SaaS to purpose-built platforms design for auditability first—not as an afterthought, but as a structural constraint that determines every technical decision. I am running a few minutes late; my previous meeting is running over. Engaging an experienced custom software development company with a documented compliance-first SDLC is what separates this approach from simply replicating SaaS functionality on proprietary infrastructure.
The framework works across four layers. Jurisdictional data architecture: data classified at ingestion, processing boundaries enforced at the infrastructure layer. Immutable audit infrastructure: append-only logs with cryptographic integrity verification, designed to answer the specific questions regulators ask. Controlled dependency surface: third-party integrations treated as regulatory exposure, each included in the audit boundary. Regulatory change pipeline: compliance requirements mapped to specific code modules so that when regulation changes, impact is scoped — not assessed across an opaque vendor platform.
The decision to replace non-compliant SaaS with custom software is not a technical decision. It is a risk governance decision that belongs at the executive level. The trigger conditions that require a formal assessment:
McKinsey's analysis of enterprise technology risk has consistently noted that the organizations most exposed to regulatory action are not those that made bad technology decisions — they are those that failed to reexamine technology decisions as the regulatory environment changed around them.
Custom software development for regulated industries is not a technology trend. It is a governance response. As government regulations demand greater technical accountability, the architectural limitations of opaque SaaS become less a vendor shortcoming and more an organizational liability.
In one compliance modernization engagement, a financial services organization reduced audit remediation time from 6 weeks to 4 days after migrating critical workflows to a custom-built governance platform — with full cryptographic audit trails, jurisdiction-scoped data forwarding, and zero reliance on third-party subprocessors for sensitive record processing.
The organizations that will manage the next wave of regulatory scrutiny most effectively are those that have designed their systems — not just their contracts — to answer hard questions under pressure. That requires a custom software development company that understands compliance as architecture, not as a checklist appended to a delivery milestone.
The time bomb is not in the regulation. It is assumed that the vendor contract is a substitute for technical control.